Introduction:
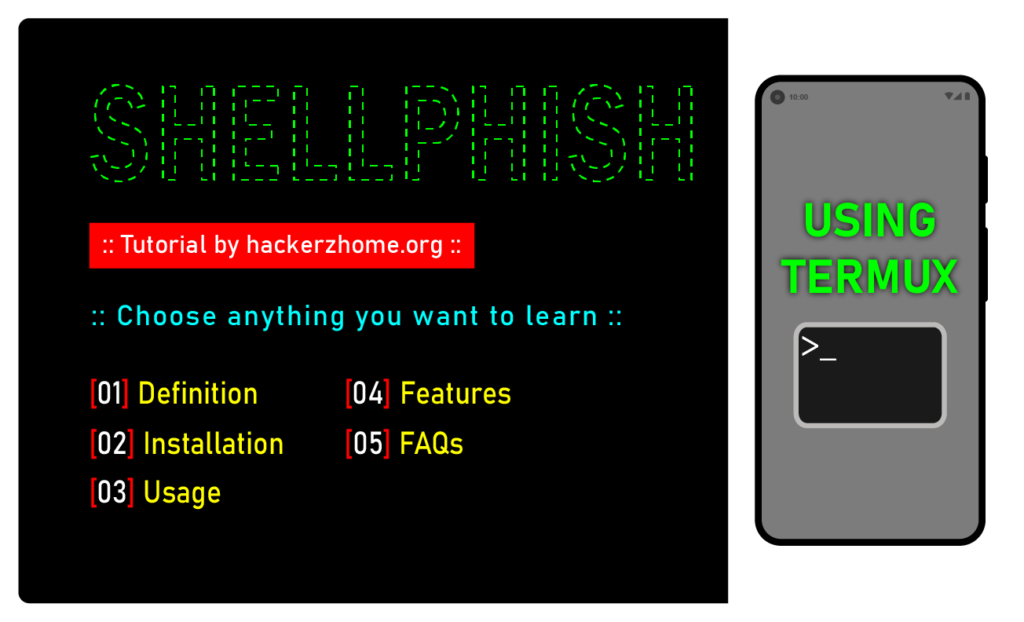
Are you familiar with the term “shellphish”? It may sound like a species of marine life, but in the world of cybersecurity, it’s a tool that can wreak havoc on your digital life. Shellphish is a type of phishing kit that allows attackers to create convincing fake login pages for popular websites such as Facebook, Instagram, and others. In this blog post, we’ll take a closer look at shellphish, how it works, and how attackers use it to steal sensitive information. Also, we will see how to install shellphish in termux to do everything from our android device.
What is Shellphish?
The name “shellphish” is a combination of the words “shell” (a command-line interface in Unix-based operating systems) and “phish” (short for phishing).
Shellphish is a type of command-line phishing kit that is designed to create fake login pages for popular websites, such as Facebook or Instagram, in order to trick users into giving away their login credentials.
The tool is typically used by hackers who want to steal sensitive information from unsuspecting victims. Once the victim enters their login credentials into the fake login page, the information is sent to the attacker, who can then use it to gain unauthorized access to the victim’s account.
Disclaimer
Working Mechanism:
The working mechanism behind Shellphish is quite simple. First, the attacker creates a fake login page using Shellphish that looks identical to the legitimate login page of a website, such as a social media platform or online banking website, and hosts it on a server. They then send this fake login page to their victim through email, text message, or other means, often disguising it as a legitimate message from the website itself.
The victim is then tricked into entering their login credentials on the fake login page. And when they hit enter, their credentials are sent to the attacker’s server. The attacker can then use these credentials to access the victim’s account, steal sensitive information, or carry out other malicious activities.
With this in mind, let’s see how to install the shellphish in termux in the next section.
Quick summary:
Well, to put it simply, Shellphish is a phishing tool that enables attackers to create fake login pages for popular websites, instead of manually coding and trick unsuspecting victims into entering their login credentials. And once you have their credentials, voila! You have access to their account.
How to Install Shellphish in Termux?
Installing ShellPhish on Termux is quite easy. But, before that, we just want to let you know, The Shellphish created by “the Linux choice” (The official creator) was removed from GitHub and it is no longer available. So will be using the modified & updated version, created by “abhirhasan2005”.
You can follow the instructions given below to install and execute it:
- Download and install the Termux app (From F-droid).
- Open the Termux app and run the following command to update and upgrade the package list:
apt update && apt upgrade- Run the following command to install the required necessary packages:
apt install git wget php unzip curl openssh -y- Run the following command to clone the ShellPhish repository:
git clone https://github.com/AbirHasan2005/ShellPhish- Navigate to the ShellPhish directory:
cd shellphish- Run the following command to give execution permission to the ShellPhish script:
chmod +x shellphish.sh- Finally, run the ShellPhish script:
./shellphish.shAfter executing the script, you will get the shellphish interface as in the image below.

We have now successfully installed and executed the shellphish tool. In the next section, we will discover how to use them properly.
How to Use Shellphish in Termux?
To use Shellphish Termux, you’ll need to follow these steps:
- Open the Termux app and navigate to the ShellPhish directory:
cd shellphish- Run the ShellPhish script:
./shellphish.sh- Select the phishing page you want to use and press enter (e.g., Facebook, Instagram, Twitter, etc.) I’m giving 2 (Instagram).
- Select the type of login you want to create and press enter (e.g., Traditional login page, blue badge verify login page, etc.) I’m giving 1
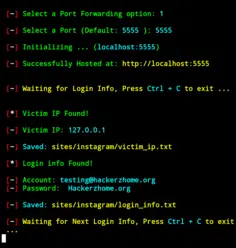
- Select the type of port forwarding option you are going to use. As this guide is not intended to attack anyone and is just an example article, I’m going to host the phishing page on my local server. But the attackers will use other options such as ngrok to host It on the live server.
- select a port in which you want the communication to happen. I’m keeping it as default. (port 5555)
That’s it. The phishing page is created and hosted successfully at localhost:5555. Take a look at the images below.
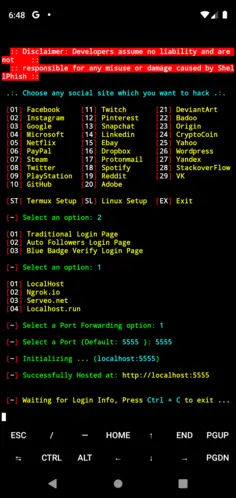
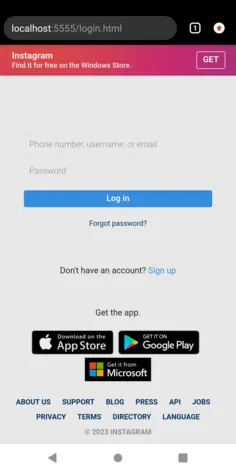
The shellphish on termux is now listening for any login info. When the target enters the credentials, you can see that here on termux.
Features of ShellPhish
ShellPhish comes with several features that make it a powerful tool for phishing. Some of its features are:
Variety Phishing Pages: ShellPhish provides several pre-built phishing pages such as Instagram, Facebook, Spotify, adobe, etc. that can be used to steal login credentials of popular social media platforms and other websites.
Customizable: If you know to code then you can modify the existing phishing pages according to your needs or create your own phishing pages.
Easy to Use: ShellPhish Termux is designed to be user-friendly and easy to use. You don’t need to have any special skills or knowledge to use it. However, having basic knowledge of Linux commands and networking can be helpful.
You may also like:
What are the Risks of Using Shellphish Termux?
While Shellphish is a powerful tool for hacking, it’s important to understand the risks involved. Here are some of the risks you should be aware of:
Legal consequences: Hacking is illegal in many countries, and using Shellphish to hack into someone’s account without their permission could result in serious legal consequences.
Personal safety: Hacking into someone’s account could lead to retaliation, harassment, or even physical harm.
Security risks: Hacking into someone’s account could compromise their personal information, putting them at risk of identity theft, fraud, or other security threats.
FAQs
No, Shellphish Termux is only available for Android devices.
Yes, ShellPhish is safe to use if you use it for ethical purposes only. However, if you use it for illegal activities, you may face legal consequences.
Yes, ShellPhish Termux can be used on all Android devices, but you have to install termux from F-droid and not from Play Store as it won’t work anymore.
Conclusion
ShellPhish is a powerful tool that can be used to create various phishing pages. However, it should be used for ethical purposes only. In this article, we discussed everything you need to know about ShellPhish, including how to install and use it, its risks, and FAQs.
As you can see, shellphish is just one of the basic tools for executing a phishing attack. But there are a lot more advanced tools available which we will see one by one in the following articles. If you have any doubts, feel free to leave a comment. Subscribe to our newsletter if you wish to follow our blog regularly. See you all in the next article. Stay tuned!