We’ve all heard of bombs, the kinds that are destructive, noisily exploding, and leave behind a wake of debris. But there’s a different type of bomb on the block, and it’s one that’s been used fraudulently by hackers for years. Don’t worry. It’s not a real bomb but kind of a virtual one – known as the ‘zip bomb.’ So, what is a zip bomb, how does it work, how to create it, and most importantly, how do you keep yourself safe? Today, we’ll be answering all these questions and more – so let’s get cracking!
Table of Contents
What is a Zip Bomb?
A zip bomb, also known as a zip of death, is an electronic file designed to crash or render data inaccessible when unzipped.
In this attack, a malicious actor sends a fraudulent compressed file, often disguised as an innocuous-looking document or image, to another user. This file contains a pattern of layers that, when decompressed by the recipient, can fill up their entire computer’s hard drive and significantly slow down or even crash the system due to the data expansion. As such, they are also called decompression bombs.
Zip bombs have been around since the 1990s but have become more widespread in modern times due to cybercriminals using this method to target unsuspecting people or companies. For a zip bomb to be successful, the victim must open the file containing the malicious payload and expand it.
When discussing whether zip bombs are harmful, there are two sides to the argument. On the one hand, some people believe that zip bombs are an effective tool for launching distributed denial-of-service (DDoS) attacks and disrupting the services of major organizations. On the other hand, many claims that these attacks are ineffective and only cause minor inconveniences compared to other malicious attack vectors.
Regardless of opinions on the effectiveness of zip bombs, it is essential to understand how these attacks work to better protect yourself from them. The following section will explain how a zip bomb attack works. before that,
Quick Recap of Key Points
- A Zip bomb is a malicious file size that is extremely small but contains multiple compressed levels, which cause extreme memory and disk usage when unzipped.
- According to a study by Avast, over 35% of all detected malware in 2020 were Zip bombs.
How Does a Zip Bomb Attack Work?
A zip bomb attack is a form of cyber attack that is also used to disable websites and servers. It involves an attacker creating and sending a malicious file that’s compressed into a small size but contains a tremendous amount of data to the victim.
When a victim decompresses the zip bomb, the victim’s computer tries to allocate memory and resources to accommodate the expanded data. In the case of a zip bomb, the decompressed data is much larger than the computer’s available resources, leading to system crashes, slowing down, or other serious problems.
For example, a zip bomb might contain a single file that is extremely large, or it might have many small files that decompress into a massive amount of data. In either case, the result is the same: the computer’s resources are overwhelmed, leading to performance problems or even system crashes.
In some cases, the malicious file may be disguised as something innocuous, like a .exe extension or .winzip file, making it easier for individuals to open. Zip bomb attacks can be executed by attaching infected files in emails, uploading them onto forums or websites, or even directly inserting them onto webmail systems. As such, it can be difficult for users to identify these malicious files before opening them.
Here is an example of a famous zip bomb – “42.zip”
42.zip
It’s a zip file with 42 kilobytes of compressed data and five levels of nested zip files in sets of 16, each with a 4.3 gigabyte file for a total of 4.5 petabytes of uncompressed data. So, when this zip file is sent, it may look like a file of size 42kb, but when it is extracted, the actual size will be 42pb.
Creating a zip bomb:
Creating a zip bomb is an unethical and potentially illegal act, as it is designed to cause harm to a computer’s resources and can potentially cause damage to the affected computer. I strongly discourage you from attempting to create a zip bomb.
However, for educational purposes, we will show you the outline of how to create one.
- Open the notepad and start typing 0. (let’s say, 1000 characters)
- Copy the zeros and paste them several times as you need.
- Once you feel enough, save the file and make copies of that text file. (let’s say, 10 files)
- Make a zip file with those copies of text files.
- Make copies of the created zip file.
- Now, make a new zip file with those copies of the zip files.
- Repeat steps 5 & 6 until you feel enough.
- That’s it.
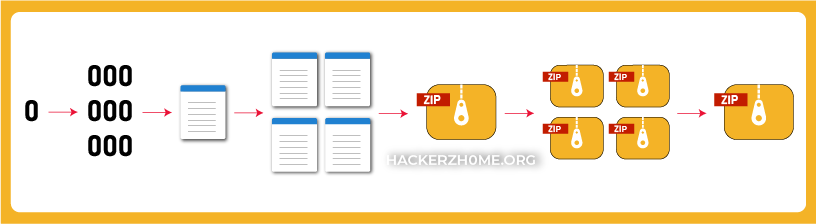
Remember, each character occupies 1 byte of memory. So, if you have a million zeros in a text file, then it occupies a million bytes of memory.
- 1 million bytes / 1024 = 976.5 KB, which is nearly 1 MB.
- So each file holds 1 MB of data, and 10 files hold 10 MB.
But the zip file, which consists of 10 files and is compressed, will only have the compressed size (let’s say 1.5 MB). It will only have the actual size (10 MB) if it’s expanded.
So, a single zip file will hold 1.5 MB of data. Make as many copies and many layers as you need.
Defending Against Zip Bomb Attacks
Although it is difficult to defend against a zip bomb attack due to its small file size, measures can still be taken. One of the most common steps is to increase the input file size limit from the default setting. Organizations and administrators should set a size threshold appropriate for the type of files that are commonly used or shared on their networks. This will help prevent malicious zip bombs from slipping past security checks, as larger zip files cannot be accepted if a smaller size threshold is set.
Additionally, organizations should use data compression technologies when transmitting large files over the network to minimize the risk of a successful attack. By compressing the files before sending them, entities can reduce their file sizes substantially, lowering their chances of becoming targets of zip bomb attacks.
Some organizations also deploy automated malware scanners at crucial points within the network, such as email server gateways or web browser filters. These tools look for any suspicious code or patterns within an incoming file and block any potentially malicious requests with minimal human effort. While this method can reduce the chances of an attacker successfully delivering a zip bomb payload, it requires significant system resources and may be ineffective if not tuned correctly.
Also read: Best Firewall for Small Business in 2023
Try using anti-virus software to scan for malicious content before opening the file. Scanning with anti-virus software is one of the most effective methods for preventing zipper bomb attacks. In general, these programs are designed to detect malicious files and programs on a computer system, then eliminate them from the computer before any data can be compromised or affected. This includes the detection of any zipper bomb attack. Even if the user unknowingly downloads an infected zip file, the anti-virus software should detect and take appropriate measures to protect the system.
Another tip is to unzip the suspected file using specialized programs such as 7-zip, known for effective unzipping of compressed files. Lastly, if you suspect that the file contains a zip bomb but cannot determine its content without opening it, consider using emulation techniques such as “sandboxing .” This isolates the program from other applications by creating an isolated environment and allows malware detection programs to uncover malicious activity before it takes effect.
Following basic precautions such as using anti-virus software and avoiding untrusted download sources can help decrease an organization’s or individual’s vulnerability to attack. While these measures may not completely eliminate all malicious traffic from entering a system through a zip bomb attack, when implemented properly, they can create several layers of defense that significantly reduce the likelihood of success for an attacker.
The Impact of Zip Bomb Attacks
Zip bomb attacks can have a devastating impact. These types of attacks occur when attackers create malicious files that, when decompressed and expanded, can fill up an entire hard drive with thousands of files in mere seconds. These attacks are especially dangerous for companies, as they can cause system crashes, degrade performance, and disrupt operations due to the lack of available storage space. Moreover, as protecting against these types of cyberattacks is very difficult in most cases, they can pose a serious threat to organizations and their data.
On the other hand, some posit that zip bombings are not always as devastating as they could be. For example, these days, many modern devices have a certain amount of storage space designed to accommodate large downloads such as videos or music albums. Therefore, if an attacker were to try to launch a zip bomb attack on your device, the large file would be blocked before it could expand and break your device’s memory limitations. As such, it is essential to remember this caveat when considering the dangers of zip bombs.
Overall, the impact of zip bomb attacks can be severe if left unchecked. However, suppose users take precautionary measures and adhere to safety guidelines outlined by their service provider or software vendor. In that case, the risk posed by zip bombs can be kept at bay.
With those impacts in mind, let’s wrap up the article with a meaningful conclusion and some FAQs.
Conclusion
We may have created a zip bomb, but do you know it is somehow useless now? Know the reason behind why I’m calling it useless.
In older days, the compression application had a feature called “recursive decompression.” Recursive decompression refers to repeatedly decompressing nested archive files until all files are extracted. In this process, a compressed archive file is extracted, and if any of the extracted files are also archive files, they are also decompressed. This process is repeated until all files have been decompressed and are no longer archived files.
The zip bomb was a bomb designed specifically for these applications. But now, most current apps do not employ recursive decompression because of zip bombs. Even today, most typical storage devices (such as your computer’s hard disk) are slow. As a result, writing a significant volume of data to the storage device would take a lengthy time. Anyone unpacking a zip bomb slowly would notice this and just stop doing it. So, the zip bomb might be useless unless the application uses recursive decompression.
Responses to Common Questions
A zip bomb, also known as a zip of death or decompression bomb, can cause significant damage to a computer system. It creates an exponentially growing file that can quickly overburden a computer’s RAM and CPU when extracted.
The resulting strain will typically cause the computer to crash, overheat and eventually shut down if not addressed. As the files keep expanding during the extraction process, the system’s resources are used until it can no longer perform its normal operations. Additionally, the errant processes created by the zip bomb can potentially be used to mount a Denial of Service (DoS) attack on other computers connected to the same network, leading to temporary disruptions in internet access. Thus, it is essential to have measures in place to protect from this type of malicious attack.
The most effective way to stop a zip bomb from reaching your computer is to have an anti-virus program running at all times and regularly updated. Anti-virus software and firewalls are essential for protecting service providers and users from malicious files like the infamous Zip Bomb.
These programs detect and block dangerous codes, filtering out malicious fragments from files before they can reach your device. Additionally, it would be best if you were vigilant with file downloads — any suspicious or unfamiliar files should be avoided. If you download a ZIP archive, scan it first using either a local or online scanning service. It’s also important to be mindful about not opening ZIP files from unsolicited sources — even if sent by someone you know — as these could contain malicious code that could compromise the security of your device.






28 Responses
Nice and informative details nice content.
I learned that A zip bomb is an electronic file designed to crash or render data inaccessible when unzipped
Good
Nice article suppose users take precautionary measures and adhere to safety guidelines outlined by their service provider or software vendor. It’s good option
Best technique but…. mostly it can be detected by antivirus…..as it only contains 0 and also packed in a zip file…
A zipbomb is a file that has been compressed to an extremely small size, but when it is uncompressed, it expands to an incredibly large size, sometimes even to several petabytes (millions of gigabytes).
Good information !!
I learnt what a zip bomb is. Zip bomb is an electronic file designed to crash or render data inaccessible when unzipped. It can also damage computer system.
Good information and blog written very well !!
“I just wanted to say that I really appreciate your in-depth analysis and thoughtful commentary on the latest tech trends and advancements. Your blog has become my go-to source for staying up-to-date on the industry, and I’m constantly impressed by your ability to break down complex topics in a way that’s easy to understand. Keep up the great work!”
Creating a zip bomb is unethical, even if you created it it’s useless because of the feature recursive decompression isn’t use at all
Honestly i just came here for netflix account but i think you have provided me with a good information .
But , even I dont think this can be good way of stealing data also if a user’s application uses recursive decompression coz people are very suspesious and even if they have open than they might notic it because it slow process ( storage )
I dont know much about these stuff but i think i have understand somewhat .
I hope for much information in future.
Lol Now i am going throught more articles
@manasmanas7864
Thank you for this update.. I really didn’t know what a zip bomb is all this while.. I really didn’t think some zip file are malicious and can cause serious harm to your operating devices and i carelessly download zip files anyhow without scanning for viruses.. Now i know better to be careful when download and decompressing zip files on my laptop and phone.
Cool article
Knowledge on zip bomb..
1.About zip bomb
2. Creating Zip bomb
3. How it attacks and having anti virus software is defending these type of bombs…
4. Impacts and conclusion is it’s useless…
But having knowledge about this is good ..?
Telegram id satish kumar siddu
Thanks for this info. I got to know that how zip bombs can be created and what precautions we can take to avoid it. And now it’s useless because of mobile phones or computer not have an old feature called Recursive decompression.
It gives complete information about zip bombs . Its intro , uses , how to use and its harms and precautions. Now I’m totally aware about this.
Good information given. Details are very clear and how you can protect your data from this bomb.. keep it up and will recommend to follow this blogger for regular update on technology and hackers related information.
Thank you for the information I have learnt about zip file in my laptop and phone now I will be able to unzip all my files easily
Where did my reply go?
Let’s make it more user friendly this time ig.
Zip bomb is just a small zip file (at least that’s what you think) but once you decompress it it would keep on decompressing untill all your storage space runs out and your pc crashes. It happens because that file contains numbers of similar zip files which also contain zip files inside of them. It’s also known as Ddos attacking. You could identify the zip bomb by using emulator and previewing it before decompressing. Thankfully it’s now useless thanks to recursive decompression used by modern phones and pc
Your tech blog is a fantastic resource for demystifying difficult technological concepts and making them more understandable to the general public.Keep up the good work.
Good points. I would add that some organizations like mine don’t allow zip files at all to be sent and received from external sites, as some mail providers don’t allow to attach zip files. Also considering that scanning is set to scan until a certain size, let’s say 1gb, because above that it would have a great impact on resource consumption. Nonetheless if it’s disguised as another file type, you would have the problem anyway. As usual, there’s not such a thing as a safe computer:-)
I have learned about zipbombs. It is a powerful way of attacking because the file to send is compressed and more difficult to defend. We should be careful so that we would not fall victim to zipbombs
Interesting article. I hadn’t heard about such malicious files ’till I read this. Now the main idea (in my eyes) is not to download suspicious or unknown files at all, even so, new decompressing applications don’t employ recursive decompression which is totally more safe than old ones, indeed companies & organizations must pay full attention to files they receive:)
A Zip bomb Is a Zipped File Virus Which Is Harmful for our System When We unzipped it and we can Protect Ourself From it by checking the size of File Before Writing it to ur disks and Before Unzipping Any File we have to remember Steps and Check it’s with antivirus and all..
Thanks
I learned from the concept of a zip bomb article was, which is a type of electronic file designed to crash or render data inaccessible when unzipped. Cybercriminals use this method to target unsuspecting individuals or companies. The file contains multiple compressed levels, which cause extreme memory and disk usage when unzipped. When the victim decompresses the zip bomb, the victim’s computer tries to allocate memory and resources to accommodate the expanded data, leading to performance problems or system crashes. The article also provides a quick guide on how to create a zip bomb, but creating a zip bomb is an unethical and potentially illegal act. It is essential to understand how these attacks work to better protect oneself from them.
Thanks for sharing information and keep going and rock
This article is very informative and helpful. I learned a lot about zip bombs and how they work. I think it’s important to be aware of this type of cyberattack and how to protect ourselves from it. Thank you for sharing this knowledge with us.
Well written.
I always knew that there’s a zip bombs technic, but I never understand why someone would use it.
I think you can detect it easily just from “browsing” the zip file content before you extract it.
and these days, every AV/EDR will catch it before you extract it.
So, a zip bomb, is a zip file that contains multiple nested zip files, that when you decompress it, it will “eat up” all your PC resources.
Thanks for explaining the method in detail. 🙂
TG: @Shak3l
Greetings,
Thanks for such an amazing and informative Article?
The article is discussing the concept of a “zip bomb,” which is a type of file that can potentially harm a computer system by overwhelming its storage and processing capabilities.
The article suggests that the effectiveness of a zip bomb may depend on whether or not the application used to unpack the file employs recursive decompression. If the decompression is done slowly, the user may notice and stop the process, rendering the zip bomb useless.
Thanks.